
Geollect featured by TradeWInds – AIS data spoofed to move 60 ships to Iran’s Bandar Abbas airport
Intelligence company Geollect tracks wide-scale manipulation over the last three months
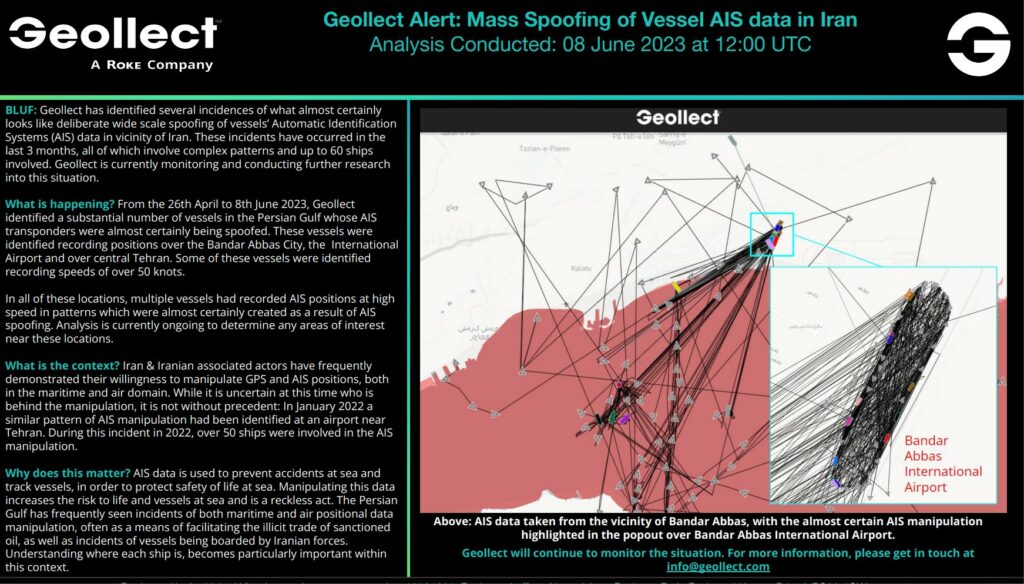
AIS data is being manipulated to show vessels doing more than 50 knots over land in Iran.
UK intelligence company Geollect has identified several incidences of what it says is almost certainly deliberate large-scale spoofing of vessels’ automatic identification systems there.
This has occurred in the last three months, involving complex patterns and up to 60 ships.
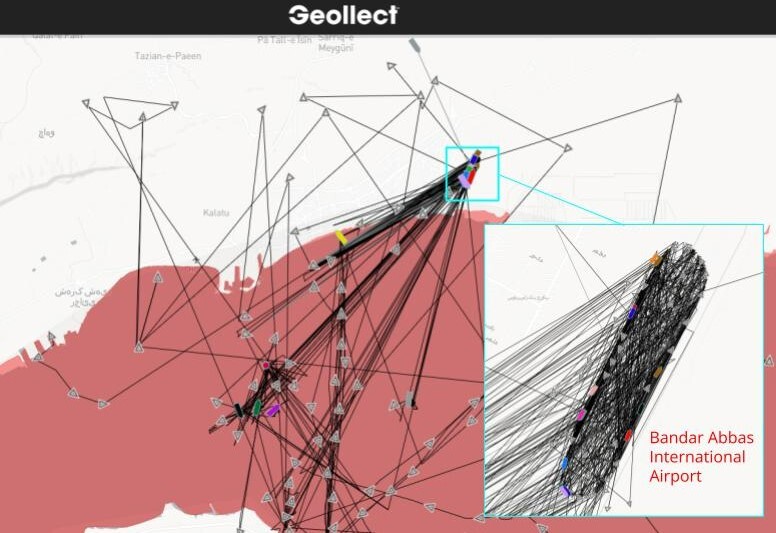
From 26 April to 8 June, Geollect identified a “substantial” number of vessels in the Persian Gulf whose AIS transponders were almost certainly being spoofed.
Positions were recorded over Bandar Abbas City and its International Airport, as well as over central Tehran.
“Geollect is currently monitoring and conducting further research into this situation,” the company said.
Iran has frequently demonstrated its willingness to manipulate GPS and AIS positions, both in the maritime and air domain.
“While it is uncertain at this time who is behind the manipulation, it is not without precedent,” Geollect explained.
In January 2022, a similar pattern of AIS manipulation had been identified at an airport near Tehran, involving more than 50 ships.
AIS data is used to prevent accidents at sea and track vessels, in order to protect safety of life at sea.
“Manipulating this data increases the risk to life and vessels at sea and is a reckless act. The Persian Gulf has frequently seen incidents of both maritime and air positional data manipulation, often as a means of facilitating the illicit trade of sanctioned oil, as well as incidents of vessels being boarded by Iranian forces,” the company pointed out.
“Understanding where each ship is becomes particularly important within this context,” Geollect added.
Last month, the company identified mass spoofing that produced a giant Russian pro-war Z symbol in the Black Sea.
The symbol had been noted off the coast of Sevastopol since 14 May.
The remote spoofing created a Z measuring 65 km in length, visible on open-source tracking software.